And if you don’t sin, then Jesus died for nothing.
Some IT guy, IDK.
- 1 Post
- 1.48K Comments
As a straight dude, I know lots of straight dudes that are represented in this picture.
We all have our little problems. ❤️
Hey! I bet you’re a really cool person!
Am I doing this right?
MVL (most valuable lemming) right here.
I’ll have to look into this. There’s a few spots around my home that I’d like to be less noisy.
 0·10 days ago
0·10 days agoOh good, I made it in time. Woo.
Thanks everyone.

 52·17 days ago
52·17 days agoYeah… That’s entirely fucked.
Guy wearing tac gear with a police branding on him, no badge in sight and covering their face like a common thug. Shoots unarmed woman in vehicle while she was trying to exit the situation in any way possible.
The only part of this that I’m thankful for is that her death was probably quick and relatively painless. Everything else about this screams hostile takeover.
I mean, that’s not new, we’ve been seeing similar bullshit forever, brought to the spotlight previously by the BLM movement. They’re just not discriminating against only POC. Now it’s anyone who isn’t them.

 7·17 days ago
7·17 days agoIf that’s what happened, they should release the body cam footage… Oh wait.

 9·17 days ago
9·17 days agoPost-mortem determination of guilt.
You were shot therefore you must have been a bad person deserving of being shot.
This is toxic thinking at it’s finest.
I’m not saying I have a better solution or a better setup at home. I’m doing something extremely similar. I would 100% say that my solution sucks… But it works.
There’s plenty of ways to do it.
I wanted to get an x16 to dual oculink 8x connector card with a matching dock, so I wouldn’t have to give up any bandwidth while getting high end graphics going, but I can’t find anything that fits that bill. So I have a riser cable bodged together with the case of my system perpetually open.
It works. I don’t love it, but I don’t have the time/money to find/buy what I feel would be more ideal. So this is what I’ve done.
I don’t want to give up half the PCIe lanes and I can’t find a way to do that with anything that’s not a riser cable.
So here I am.
Thanks, I always wondered how other people solved this exact problem.
Now I know.
Poorly.
Carry on.

 1·27 days ago
1·27 days agoI won’t argue with you there.
My entire point for my comment from earlier is that I don’t know what a “healthy weight” is for that person. I also won’t assume that “under 200lbs” is either above, or below, that amount.
I didn’t make any assumptions about it. My comment being “if it makes you happy?” Is more of a question of, if being under that weight is bringing you happiness. Because I will neither speculate, nor assume, what a healthy body weight is for that person, and I’m not going to ask for their private medical information on what a healthy weight is, so my only hope is that they’re happy about the change.
I probably could have said it better, but it would not have been as terse.
I find that the more terse I can be, the better my comments tend to do. It would seem that most people don’t want to read an entire encyclopedia for an answer to a relatively basic question. The issue I have is that, when I include context, I want to make as few assumptions about the reader as I can. About what they know or don’t know, or if they are familiar with medical terms or caught up in colloquialisms. Clarifying each point to the extent I need to in order to accommodate for those assumptions I am not making, is a verbose task.

 4·29 days ago
4·29 days agoGas stoves have a place, and I’m not about to take away anyone’s choice on the matter. With all that being said, to the title of this article, I say “duh”… Honestly, who thought that cooking using an open flame inside your home was somehow safer than the alternative?
I use electric, I’ve pretty much always used electric. I will continue to use some form of electric stove. I want to have complete control over the heat going into my cookware, and while it may not be as flashy or as quick to use electric, I can’t see any situation where electric would not be safer.

 1·29 days ago
1·29 days agoPossibly.
I wasn’t about to jump to that conclusion.
People just focus so much on a number on a scale, when the focus should be on being healthy. Sometimes weight is a part of that, sometimes not.
I’ve met people that couldn’t weigh more than 100lbs soaking wet, yet they’re unhealthy to high hell, and frequently paying the (medical) price for that. Meanwhile, I’ve known people who can’t, by any means, get below 200lbs and they’re in near perfect health.
Weight does not equal health.
Being healthy doesn’t require that you are a particular weight.

 403·29 days ago
403·29 days ago“when I’m wrong, I say I’m wrong” … This is a statement of intent. That you will say you’re wrong, when you are wrong…
This is not an admission of fault. This is not saying “I am wrong”.
Way to dance around saying the one thing that actually matters in this whole damn thing… And… You’re sorry? I don’t want your sorry. What will your sorry do for everyone fucked over by the rapist convict you put in the Whitehouse?
Fuck you. I hope the leopards eat the rest of you too.

 16·29 days ago
16·29 days agoI can’t stop laughing about it, though I hope that Kitty was able to get back to a more typical size.
 11·29 days ago
11·29 days agoI understand your reasoning, but please God no.

 37·29 days ago
37·29 days agoWeight thing: meh, if it makes you happy?
Glucose thing: fuck yeah dude.
Jesus. I’ve administrated a bunch of Adobe accounts in various ways and it’s not always straight forward to tell what licenses are in use and by whom. These pencil necked fucktards thought they somehow knew better than the government IT guys, what’s in use and what isn’t…
Incredible.
In any case, I’m glad their eating their own chow. They made this bed and now hopefully, they’re about to get fucked in it.
I somehow doubt it, but I can dream Harold.



Having children demonstrates one of two things: wealth, or intelligence.
On one hand, if you can afford to overcome the obstacles, children seem like a good idea, usually from family wealth, since nobody is going to become wealthy. You’re either born into it, or you’re extremely lucky and you win the lotto or something, which is so unlikely it’s hardly worth mentioning.
On the other hand, if you’re too dumb to know how fucked we all are, or you’re too dumb to use protection in some form… Well. Yay kids? Idk.
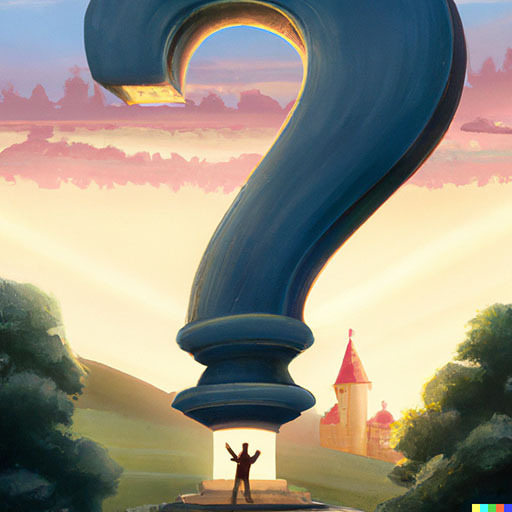
Everyone with somewhere close to an “average” IQ, or better, who isn’t part of the upper class with family wealth, is basically represented here.